
Mobile technology has changed every facet of the way businesses operates and never before in history has that change occurred so fast and so drastic. More than 201 ago, employees used to talk with each other using brick-like telephones. Fast forward today; the modern office is often filled with people who cannot be separated to their smartphones which computing power is more than all of NASA did have when they started sending a man to space.
However, despite these advancements, the concern about data security is still at an all-time high. As the use of the mobile device in the workplace becomes more rampant, more and more employees are now allowed to use their mobile device for different tasks – including those that involve sensitive customer data such as credit card numbers. Furthermore, as the number of devices being managed in the enterprise increases each year, the number of companies which are at risk of cybersecurity issues also increases drastically.
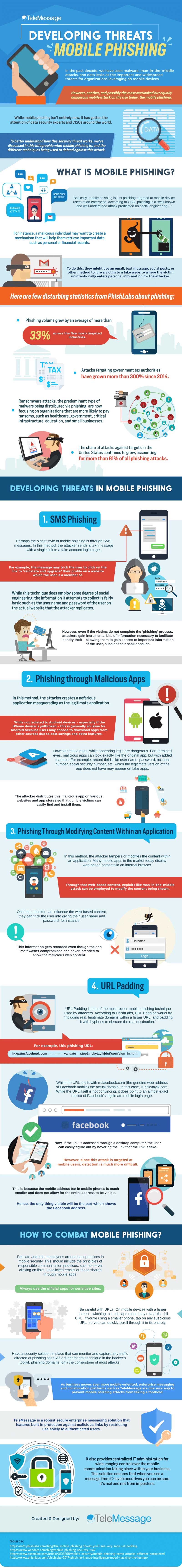
One of the methods being used by hackers to take advantage of the weaknesses of mobile environment is phishing. Phishing is a type of cyberattack which attempts to collect sensitive user information by masquerading as a trustworthy entity – such as a fake website – to convince users to provide their information – either by opening emails and installing applications on their mobile devices.
Over the course of time, cybercriminals have developed several sophisticated methods to make mobile phishing more effective. To give you more insights about the latest developments in one of the most dangerous threats in the mobile environment, here are the key takeaways from the infographic below from TeleMessage.
- SMS phishing
- Phishing through malicious apps
- Phishing through modifying content within an application
- URL padding
To learn more about the developing threats in mobile phishing, check out the infographic below.
This Infograph is shared here after legal permission from TeleMessage













Be the first to write a comment.