
The virus, being a foremost malicious code, has made many devices vulnerable; irrespective of the OS installed on it. Being quite versatile in nature, the virus has the proficiency to replicate its look and resembles like the program or files which the device users access the most such as web browser app or antivirus software application, that are already installed on the device. Once gets intruded in the device boot sector, it records the information about how the PC or Smartphone device works and take action accordingly to engulf the entire device so that infection can spread to other devices connected with it through network; eventually making it vulnerable to use.
Unexpected virus attack does not allow the user to perform a task on the device. The backup files get corrupted due to which device cannot boot or start-up, due to the ineffective performance of the Operating system. The impact of virus attack is so impulsive that it adversely affect the performance of files accessibility as well as software applications. With various brands developing antivirus product, the virus files are traced immediately and removed in quick time. But users do not upgrade the software products as its brand reveal new features and functionalities. Only due to this, the application gets obsolete and does not perform as per its efficiency.
Here are top 5 sources of virus attack that often make the people frustrated.
- Cracked Software
- Attachments downloaded from spam emails
- Access to untrusted websites and applications
- Using CD/DVD to boot PC/Laptop device
- Downloaded applications from third party-websites
Internet users access numerous websites on their device on daily basis and are not aware of the insecure websites through which spyware, adware, and ransomware intrude in the device. These files create a deadlock in the PC or Smartphone device. The people also search for downloadable software applications that can provide ease in performing tasks that often make the things worst as it one of the top sources of virus attack.
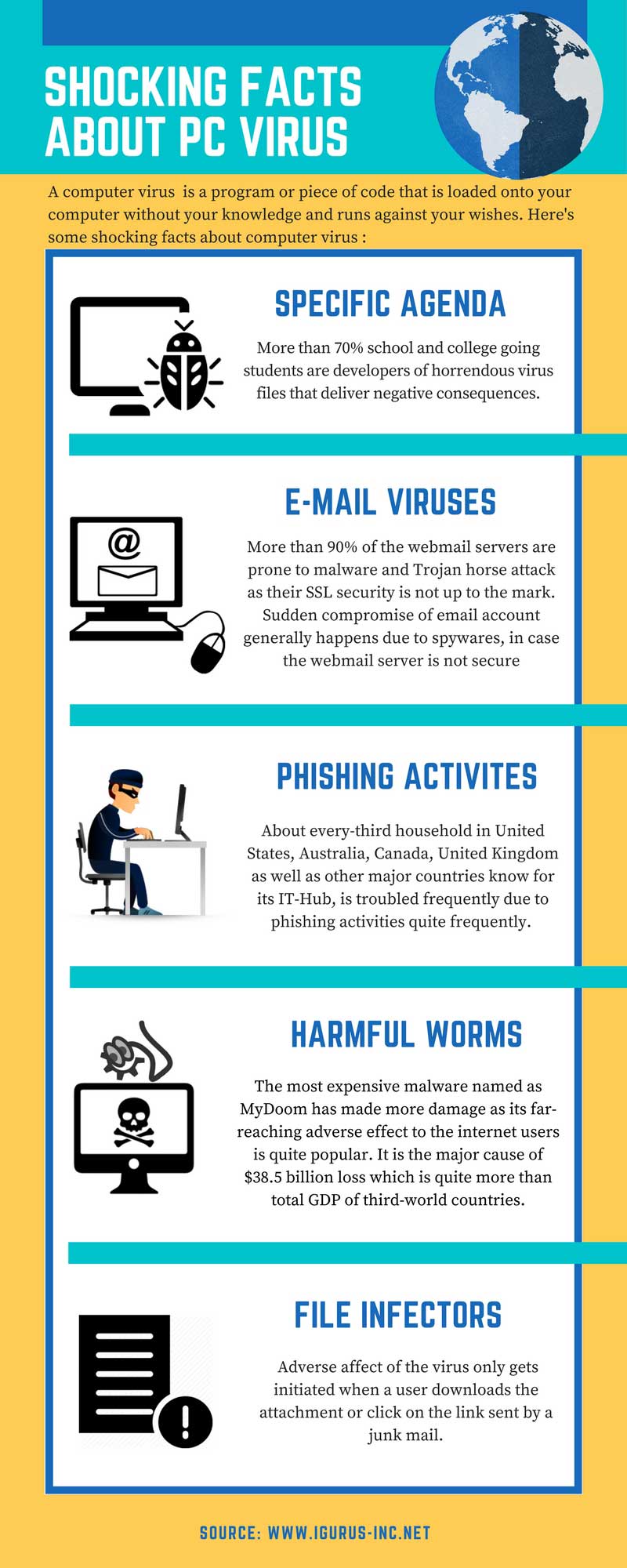
This Infograph is shared here after legal permission from iGurus-inc.net.












Hi,
This blog is awesome and very informative too. You have shared really worthy points regarding security. You have told us some actual facts about computer viruses which might be people will not aware about. So therefore your blog is very useful.
Thank you for the post
Open Source Solution Experts (opensourcesolutionexperts.com)
Welcome here and thanks for reading our article and sharing your view.