More enterprises today are adopting AI into their operations to optimize workflows and stay competitive. The shift provides several significant benefits, but it makes identity verification critical. In the absence of strong verification, AI systems that are used in tasks like employee onboarding, vendor authentication, etc., can be misled or exploited.
A huge number of businesses today find it challenging to detect fraudsters during onboarding. The cutting-edge identity verification combines enterprise-grade security with AI-powered automation. This allows enterprises to validate digital identities in real-time, decrease fraud, and stay compliant across complex workflows. In the following sections, we will first know the meaning and importance of enterprise-grade identity verification and then go through its components and steps involved in the implementation.
Table of Contents
Understanding Enterprise-Grade Identity Verification:
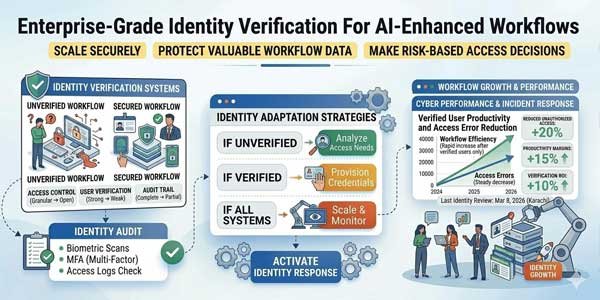
Enterprise-grade identity verification involves advanced processes and systems that authenticate devices, individuals, or AI agents working within an organization. Basic verification methods (for example, static tokens or passwords) provide weak security. On the other hand, enterprise-grade solutions utilize biometrics, digital certificates, multi-factor authentication, and more. The purpose is to ensure that each identity that deals with enterprise systems is genuine.
It is important to verify identity so that enterprises stay protected against compliance breaches, data misuse, and fraud. Many businesses face hassles while discovering fraudulent identities during onboarding. This is why a robust enterprise-grade verification system is imperative.
The solution is especially significant for AI-enhanced workflows. The reason is that AI agents deal with tasks like vendor verification, customer onboarding, employee access, transaction validations, etc. While dealing with these tasks, they need verified digital identities to avoid misuse. In the absence of strong identity controls, AI systems can be misused, tricked, or granted excessive access. As a result, this can create serious compliance and security risks.
The addition of enterprise-grade verification to AI workflows builds trust, keeps organizations accountable, and protects operations. They accomplish all these without compromising on the speed and scalability.
What Makes Up the Enterprise-Grade Identity Verification?
The section below discusses some key components that work together to make sure the identity verification is effective and reliable.
1.) Multi-Factor Authentication (MFA):
MFA asks users to carry out two or more checks (for example: entering a password, scanning a fingerprint, or token). Even if one is stolen, the others keep the system secure.
2.) Biometric Verification:
Biometrics (like fingerprint scanning, facial recognition, or voice authentication) give strong identity assurance. They are difficult to forge and help ensure that the right person is accessing sensitive workflows.
This element offers a highly secure, risk-free, swift method of verifying identity. Certain companies now use Liveness Detection to avoid deepfake attacks, tampering, and fake documents.
3.) Digital Certificates and Credentials:
To authenticate users, devices, and applications, enterprise systems usually rely on digital certificates and trusted credentials. These proofs keep communication secure and stop identity theft in AI workflows.
4.) Continuous Monitoring:
This involves continuously tracking use behavior and adapting authentication when risks appear (like suspicious activity or unusual logins). This helps stop fraud in real-time.
5.) Regulatory Frameworks:
Following rules (like GDPR and financial regulatory standards) is necessary for enterprise solutions. They help organizations stay compliant and protected from penalties.
Reasons to Carry Out Enterprise-Grade Identity Verification:
Going through the section below will help you understand how important it is to conduct enterprise-grade identity verification to deal with AI workflows.
1.) Avoids Fraud and Identity Theft:
One of the key reasons enterprises adopt the latest identity verification is to prevent malicious actors from exploiting weak systems. A significant number of businesses face difficulty in detecting fraudulent identities while onboarding. This can result in loss of finance as well as reputation.
Using a verification system means only genuine users can access the workflows. Consequently, the risks related to identity theft and fraud are cut down.
2.) Promises Trust:
AI workflows are now commonly seen in tasks like vendor validation, customer onboarding, and more. If identities are verified, data does not get manipulated. Eventually, it keeps enterprises confident that their implemented AI workflows operate on precise data.
3.) Maintains Necessary Compliance:
Enterprises in regulated industries must adhere to identity verification as well as data protection standards. Conducting audit trails and reporting assists them meet these standards and thus they can stay accountable.
4.) Keeps up Customer Trust:
The first communication between a business and customers is usually through identity verification. Smooth, secure onboarding establishes trust, whereas weak ones hurt business reputation. Tools used for enterprise-grade identity verification balance security and user experience.
Steps to Implement this Verification System:
The implementation of enterprise-grade identity verification follows a structured approach as outlined below to balance compliance, security, and user experience.
Step-1: Build Trust With Secure Data Collection
First, establish a trustworthy method of collecting identity data (for example: biometrics, digital credentials). This process should ensure data accuracy and safeguard sensitive information via secure channels and encryption.
Step-2: Validate Identity
After collecting the data, enterprises should validate it against reliable sources. This covers biometric matching, document verification, or verifying against state and financial records. Validating identity ensures that the entity or person is genuine and not using stolen or fake identities.
Step-3: Add Multi-Factor Authentication (MFA)
The addition of MFA boosts security as it requires multiple verification factors (like biometrics, one-time codes, or passwords). This step lowers the risk of illegal access, even when one of the factors is compromised.
Step-4: Continuous Monitoring for Real-time Defense
One-time checks are not useful for enterprise-grade systems. This is because they need to keep monitoring behavior and apply adaptive authentication when something looks suspicious, like unusual logins. It helps block fraud in real-time.
Step-5: Integration with AI Workflows
This step involves integrating verified identities in every workflow, like vendor authentication, onboarding, and financial consents. With this step, AI systems keep working on trustworthy data, and fraudulent actors can’t manipulate them.
Step-6: Maintain Compliance
The last step suggests that enterprises should align identity checks with regulations like HIPAA, GDPR, or financial compliance standards. The step involves keeping audit trails, reporting, and governance to meet legal requirements.
Challenges Enterprises Face Without Identity Verification:
Without identity verification, enterprises encounter fraud incidents, compliance failures, poor trust, and more. Here are some key challenges discussed.
1.) Fraud Risks in Onboarding
In the absence of strong identity checks, enterprises face difficulty in detecting stolen or fake identities during vendor or customer onboarding. The latest reports suggest that 31% of businesses face challenges regarding fraud when conducting employee onboarding.
2.) Exploitation of AI Systems
Relying on unverified identities means that AI workflows can be exploited or misled. This situation will allow malicious actors to illegally access data or feed false data into automated processes.
3.) Failure of Zero-Trust Security
Each user or agent should be authenticated in enterprise AI workflows. Not carrying out identity verification means that the ‘never trust, always verify’ principle will no longer work. This will make systems vulnerable to unauthorized activities.
4.) Governance and Compliance Risks
Weak identity verification checks put companies at risk of breaching rules. This is especially seen in industries like healthcare and finance, where audit trails and verified identities are required.
Conclusion:
Enterprise-grade identity verification serves as the foundation of safe and reliable AI-enhanced workflows. Enterprises can focus on biometrics, compliance alignment, continuous monitoring, and other strategies as discussed above to control fraud, stay compliant, and maintain consumer trust. AI systems are now increasingly used in onboarding, transaction approvals, access management, etc. This means implementation of robust identity verification can make sure automation operates on reliable, verified data. The implementation will boost security and also empower enterprises to confidently scale AI adoption. Eventually, it will reduce the gap between accountability and efficiency in the enterprises.

 About the Author:
About the Author:












Be the first to write a comment.